Pursuit vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
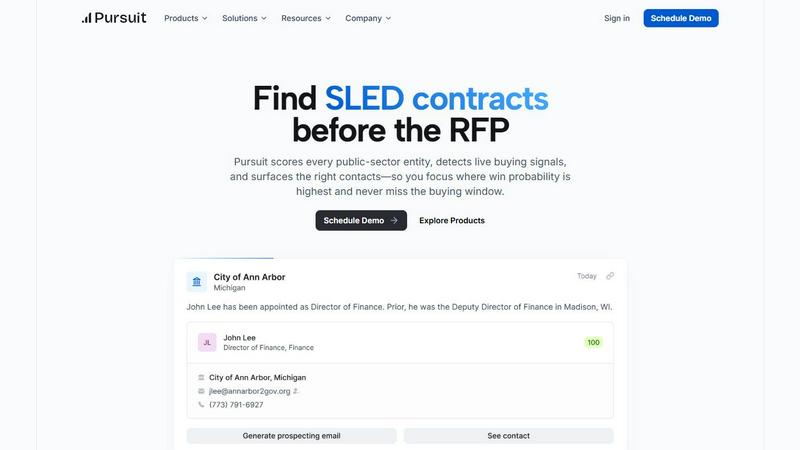
Pursuit
Win SLED contracts before RFPs drop with AI that finds hidden buying signals.
Last updated: February 28, 2026
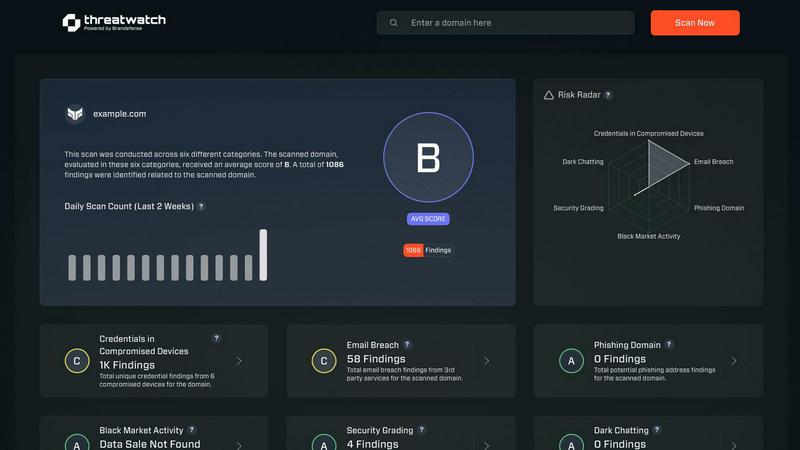
Threat Watch
Instantly evaluate your cybersecurity health and uncover threats with Threat Watch's actionable insights today!.
Last updated: March 1, 2026
Visual Comparison
Pursuit
Threat Watch
Feature Comparison
Pursuit
Pre-RFP Signal Intelligence
Pursuit's core AI engine scans and analyzes documents from over 110,000 SLED entities to surface genuine buying signals long before formal procurement begins. It identifies budget approvals, contract expirations, new strategic initiatives, and project discussions hidden in meeting minutes, giving your team a 6-18 month head start. This transforms your approach from reactive RFP-chasing to proactive, strategic engagement, allowing you to shape deals before your competitors even know they exist.
Actionable Contact & Account Intelligence
Go beyond basic directories. Pursuit provides continuously enriched account profiles with accurate org charts, incumbent vendor details, past contract values, and specific procurement processes. It automatically identifies and prioritizes the right 4 million+ contacts, scoring their relevance and influence. This ensures your outreach is hyper-targeted, based on real-time roles and involvement in active projects, not outdated lists.
Native CRM & Workflow Integrations
Pursuit is built for seamless operation within your existing tech stack. It offers bi-directional sync with major CRMs like Salesforce and HubSpot, ensuring enriched account data, buying signals, and new contacts flow automatically without manual entry. This native integration extends to marketing platforms (Marketo, LinkedIn Ads) and sales engagement tools, creating a unified intelligence layer across your entire go-to-market team.
Role-Specific Intelligence Dashboards
The platform delivers tailored insights for every persona. Sales leaders get team-wide signal visibility and territory coverage analysis. AEs get instant meeting prep via a Chrome extension. BDRs receive daily prioritized call lists. Customer Success monitors for renewal and churn signals. This ensures every team member acts on the same powerful intelligence, but in the context that matters most for their role, driving coordinated execution.
Threat Watch
Real-Time Cyber Threat Monitoring
Stay ahead of potential threats with real-time monitoring that keeps you informed about emerging risks and vulnerabilities. Threat Watch continuously scans your environment, alerting you to any suspicious activities that could compromise your security.
Automated Risk Assessments
Say goodbye to manual risk evaluations. Threat Watch automates the risk assessment process, providing you with timely insights into your organization's vulnerabilities and exposures. This feature allows security teams to prioritize their efforts effectively and allocate resources where they are most needed.
Comprehensive Asset Evaluation
Understand your cyber landscape with an in-depth analysis of your critical assets. Threat Watch evaluates every aspect of your cybersecurity posture, providing a complete view of your strengths and weaknesses, enabling informed decision-making.
Dark Web Monitoring
Uncover threats lurking in the shadows with our Dark Web Monitoring feature. Threat Watch scans dark web forums and marketplaces for stolen credentials and compromised accounts, giving you the ability to take action before these threats affect your organization.
Use Cases
Pursuit
Accelerating New Logo Acquisition for Sales Teams
Sales and Business Development Reps use Pursuit to stop cold calling blindly. The platform delivers daily alerts on high-intent signals within their territory, such as budget approvals for relevant projects or leadership changes at key agencies. With one-click ability to add prioritized accounts to sequences and full meeting intelligence, teams have reported a 47% increase in qualified pipeline and a staggering 20% cold call conversion rate by engaging with context and perfect timing.
Powering Strategic ABM Campaigns for Marketing
Marketing teams leverage Pursuit to build Account-Based Marketing campaigns rooted in real buying signals, not firmographics. By syncing audiences of in-market accounts—those with approved budgets, expiring contracts, or new initiatives—directly to platforms like LinkedIn, Marketo, or HubSpot, marketers can deliver hyper-relevant content. This signal-driven approach has led to a 2.4x lift in ABM campaign conversion rates, as messaging aligns directly with the public entity's current needs and budget cycle.
Forecasting with Confidence for Sales Leadership
Sales leaders and VPs utilize Pursuit to move beyond gut-feel forecasting. The platform provides a clear view of which buying signals are being tracked by each rep, identifies coverage gaps across vast territories, and uses real procurement indicators to predict pipeline health. This intelligence allows leaders to coach based on activity around real opportunities, allocate resources strategically, and forecast revenue based on tangible, early-stage engagement, leading to more predictable growth.
Protecting & Expanding Revenue for Customer Success
Customer Success managers configure Pursuit to monitor their existing accounts for both renewal and churn signals. Alerts for budget cuts, leadership changes, or competitor RFPs at their customer agencies provide a 90-180 day head start on renewal conversations. This proactive intelligence enables CSMs to mitigate risk, align value with the customer's evolving priorities, and identify expansion opportunities, resulting in 3x faster renewal identification and stronger retention rates.
Threat Watch
Small Business Cybersecurity Enhancement
Small businesses often lack the resources for extensive cybersecurity measures. Threat Watch provides an affordable and effective way for them to identify vulnerabilities and enhance their security posture, ensuring they are protected from cyber threats.
Enterprise-Level Risk Management
Large enterprises face complex security challenges. Threat Watch streamlines risk management processes by providing real-time insights and automated assessments, allowing security teams to focus on strategic initiatives while effectively managing risks.
Incident Response Preparation
Being prepared for an incident is crucial. Threat Watch equips organizations with the tools needed for rapid incident response. By continuously monitoring threats and vulnerabilities, companies can respond swiftly and effectively to mitigate damage.
Compliance and Regulatory Assurance
Organizations need to comply with various cybersecurity regulations. Threat Watch helps in maintaining compliance by providing detailed reports and assessments, ensuring that organizations meet necessary standards and protocols.
Overview
About Pursuit
Stop playing the guessing game in public sector sales. Pursuit is the AI-powered intelligence platform that's completely revolutionizing how businesses sell to state, local, and education (SLED) governments. For government contractors, SaaS companies, and any business targeting this $2 trillion market, the old playbook is broken. The sales cycle is notoriously opaque, slow, and filled with missed RFPs buried in endless manual research. Pursuit shatters that barrier. It acts as your 24/7 AI analyst, continuously monitoring over 110,000 public entities. Using advanced AI, it scans millions of documents—budget proposals, council meeting transcripts, contract databases—to uncover live buying signals 6-18 months before an RFP ever drops. This isn't just data aggregation; it's actionable intelligence. Pursuit scores opportunities by win probability, surfaces the exact right contacts from a database of over 4 million, and pushes everything directly into your CRM. The mission is clear: remove all friction from public sector sales. This is why industry leaders from Flock Safety to OpenGov rely on Pursuit to supercharge pipeline generation, achieve up to a 6.6x pipeline increase with 0 new hires, and turn public sector complexity into their single greatest competitive advantage. Stop being an outsider and start showing up as the incumbent.
About Threat Watch
Threat Watch is a revolutionary cybersecurity intelligence platform meticulously crafted to protect organizations from the dynamic and increasingly complex landscape of cyber threats. In an age where digital assets are constantly under siege, Threat Watch assesses your organization's critical assets, vulnerabilities, and exposures, offering a thorough overview of your cyber health. Its strength lies in real-time insights and automated assessments that empower organizations to quickly identify, prioritize, and mitigate risks. Designed for everyone from small businesses to large enterprises, Threat Watch is the go-to solution for those looking to enhance their cybersecurity defenses. With its intuitive interface and powerful analytics, security teams can make informed, data-driven decisions, ensuring threats are neutralized before they can inflict damage. Experience cybersecurity like never before and uncover your organization's cyber health in a flash with Threat Watch.
Frequently Asked Questions
Pursuit FAQ
What types of buying signals does Pursuit actually detect?
Pursuit's AI is trained to identify a wide range of high-intent signals from public documents. This includes budget line items for new projects, discussions in city council or school board meeting minutes about technology needs, contract expiration notices, RFI (Request for Information) publications, and leadership changes at agencies. It connects these disparate data points to paint a clear picture of upcoming procurement opportunities long before the formal RFP is released.
How does Pursuit ensure data accuracy and freshness?
Pursuit maintains a 94% data accuracy rate through continuous, automated enrichment. The platform's systems constantly monitor and cross-reference sources from over 110,000 entities. When a contact changes roles, a new budget is passed, or a meeting transcript is published, the relevant account and opportunity profiles are updated in real-time. This ensures your team is never working from stale or incorrect information, which is critical in the dynamic SLED market.
Can Pursuit integrate with our existing CRM and sales stack?
Absolutely. Pursuit is built with seamless integration in mind. It offers native, bi-directional integrations with Salesforce and HubSpot, allowing enriched account data, contacts, and buying signals to flow automatically into your existing records. It also syncs with marketing automation platforms and sales engagement tools, ensuring the intelligence is actionable within the workflows your team already uses daily, without requiring engineering support.
Is Pursuit suitable for companies new to selling to the SLED market?
Yes, Pursuit is incredibly valuable for both SLED veterans and newcomers. For new entrants, it acts as a force multiplier, instantly providing the market knowledge, procurement pathways, and key contacts that would otherwise take years to build organically. It demystifies the complex landscape, revealing where and when to engage. This levels the playing field and allows new players to compete effectively by focusing their efforts on real, in-market opportunities from day one.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for organizations of all sizes, from small businesses to large enterprises. Its scalable features make it an ideal solution for anyone looking to improve their cybersecurity defenses.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced scanning techniques to monitor various dark web forums and marketplaces for stolen credentials and compromised accounts. This proactive approach ensures organizations can act before threats materialize.
Can Threat Watch integrate with existing security tools?
Yes! Threat Watch is designed to seamlessly integrate with a wide range of existing security tools and platforms, enhancing your current cybersecurity framework without disrupting your operations.
Is there a free trial available for Threat Watch?
Absolutely! Threat Watch offers a free scan to help organizations assess their cybersecurity health. This allows potential users to experience the platform's capabilities before making a commitment.
Alternatives
Pursuit Alternatives
Pursuit is an AI-powered business intelligence platform that helps companies sell to state, local, and education (SLED) governments. It automates the hunt for contracts by scanning public documents for early buying signals, long before a formal RFP is announced. This category of software is essential for any business serious about tapping into the massive public sector market. Users often explore alternatives for a few key reasons. Budget constraints or specific pricing models can be a factor, as can the need for different feature sets or integrations with their existing sales stack. Some teams might be looking for a platform that covers additional markets beyond SLED or offers a different user experience. When evaluating other options, focus on core capabilities. Look for robust, AI-driven signal detection that goes beyond simple keyword alerts. The quality and depth of the contact database is critical, as is the platform's ability to seamlessly push qualified leads into your CRM. Ultimately, the right tool should turn the complexity of public sector sales into a clear, actionable pipeline.
Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence platform designed to assess organizations' cybersecurity health and identify potential threats. As a vital tool for businesses seeking to enhance their security posture, it provides real-time insights and automated assessments to safeguard assets against the evolving landscape of cyber threats. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with their existing platforms. When exploring alternatives, it is essential to consider features such as real-time monitoring, ease of use, and the ability to integrate with your current security solutions. Choosing the right cybersecurity solution can be daunting, especially with the myriad of options available. Prospective users should look for platforms that offer comprehensive vulnerability analysis, robust analytics, and user-friendly interfaces. The ideal alternative should not only meet your organization's security needs but also provide a seamless experience for your security teams, enabling them to focus on mitigating risks effectively.
