Karolium vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
Join Gartner-recognized Karolium to build custom AI apps 10x faster with zero code.
Last updated: February 28, 2026
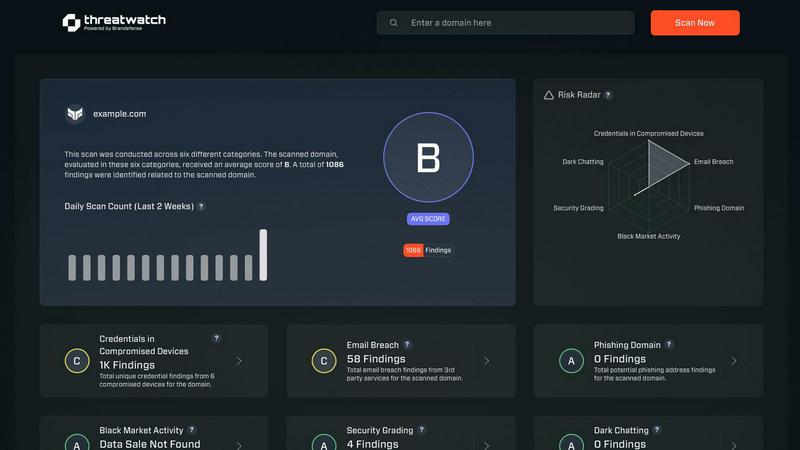
Threat Watch
Instantly evaluate your cybersecurity health and uncover threats with Threat Watch's actionable insights today!.
Last updated: March 1, 2026
Visual Comparison
Karolium

Threat Watch
Feature Comparison
Karolium
Unified Zero-Code Platform
Karolium combines iPaaS, aPaaS, oPaaS, and AIPaaS into a single, code-free environment. This unified architecture allows enterprises to build, extend, integrate, and customize intelligent business solutions without writing a single line of code, breaking the dependency on developer teams and accelerating delivery by 10X.
Pre-Composed Value Chain Solutions
Accelerate time-to-value with a suite of ready-to-use, enterprise-grade modules. These pre-built solutions cover critical areas like Supplier Collaboration, AI-Infused Demand Forecasting, Smart Compliance, and Unified Master Data Management, allowing you to deploy and customize complex functionality rapidly.
Built-In AI & Predictive Intelligence
Move from reactive operations to proactive strategy with Karolium's embedded AI capabilities. The platform offers built-in predictive and prescriptive solutions, enabling you to create AI-driven applications for forecasting, lead time prediction, asset monitoring, and image recognition seamlessly within your workflows.
Boundless Customization & Composability
Experience limitless flexibility with complete composability. Every pre-packaged module and user-composed application can be tailored endlessly to fit your exact business processes. The platform supports unlimited users and delivers new, enhanced modules with every quarterly release, ensuring continuous growth.
Threat Watch
Real-Time Cyber Threat Monitoring
Stay ahead of potential threats with real-time monitoring that keeps you informed about emerging risks and vulnerabilities. Threat Watch continuously scans your environment, alerting you to any suspicious activities that could compromise your security.
Automated Risk Assessments
Say goodbye to manual risk evaluations. Threat Watch automates the risk assessment process, providing you with timely insights into your organization's vulnerabilities and exposures. This feature allows security teams to prioritize their efforts effectively and allocate resources where they are most needed.
Comprehensive Asset Evaluation
Understand your cyber landscape with an in-depth analysis of your critical assets. Threat Watch evaluates every aspect of your cybersecurity posture, providing a complete view of your strengths and weaknesses, enabling informed decision-making.
Dark Web Monitoring
Uncover threats lurking in the shadows with our Dark Web Monitoring feature. Threat Watch scans dark web forums and marketplaces for stolen credentials and compromised accounts, giving you the ability to take action before these threats affect your organization.
Use Cases
Karolium
Augmenting Legacy ERP & CRM Systems
Businesses frustrated by the limitations of their core ERP or CRM use Karolium to augment functionality without a costly replacement. They rapidly build and attach custom modules for procurement, contract manufacturing, or service management, creating a tailored, intelligent ecosystem that works with their existing investments.
Rapid Supply Chain Digitization
Organizations modernize their supply chain by deploying Karolium's pre-composed modules for supplier collaboration, warehousing, and AI-driven demand forecasting. This enables real-time coordination across all layers, reduces lead times, and mitigates market volatility without point-to-point integrations or hefty licensing fees.
Building AI-Driven Operational Applications
Teams aiming to leverage AI for tangible outcomes use Karolium's code-free AIPaaS environment to create intelligent applications. Examples include building an AI-infused asset monitoring system with digital twin technology or an image recognition tool for automated quality checks, all with seamless integration.
Accelerating Custom Application Development
Companies needing specific applications that off-the-shelf software can't provide use Karolium to become self-sufficient. They bypass IT backlogs and rapidly compose custom applications for unique workflows like appointment and yard management or specialized compliance reporting, achieving in weeks what used to take years.
Threat Watch
Small Business Cybersecurity Enhancement
Small businesses often lack the resources for extensive cybersecurity measures. Threat Watch provides an affordable and effective way for them to identify vulnerabilities and enhance their security posture, ensuring they are protected from cyber threats.
Enterprise-Level Risk Management
Large enterprises face complex security challenges. Threat Watch streamlines risk management processes by providing real-time insights and automated assessments, allowing security teams to focus on strategic initiatives while effectively managing risks.
Incident Response Preparation
Being prepared for an incident is crucial. Threat Watch equips organizations with the tools needed for rapid incident response. By continuously monitoring threats and vulnerabilities, companies can respond swiftly and effectively to mitigate damage.
Compliance and Regulatory Assurance
Organizations need to comply with various cybersecurity regulations. Threat Watch helps in maintaining compliance by providing detailed reports and assessments, ensuring that organizations meet necessary standards and protocols.
Overview
About Karolium
Stop wrestling with rigid, off-the-shelf software and endless, costly developer backlogs. Karolium is the Gartner & IDC Recognized platform that's going viral for a reason: it delivers enterprise-grade technology and business solutions at a mind-blowing 10X speed. This isn't just another tool; it's your unified zero-code command center for true digital transformation. Designed for forward-thinking businesses, Karolium empowers you to rapidly build, customize, and deploy codeless applications that perfectly fit your unique workflows. It's a full-scale enterprise intelligence platform that seamlessly augments your existing ERP, CRM, or legacy systems—no disruptive rip-and-replace needed. With its unique combination of iPaaS, aPaaS, oPaaS, and AIPaaS capabilities, Karolium provides ready-to-use, pre-composed modules for everything from supply chain to asset management. Imagine extending your core systems with intelligent, AI-driven modules in weeks, not years. Join the thousands ditching slow custom development and inflexible software. With an active SaaS subscription offering continuous innovation, unlimited users, and boundless customization, Karolium is the smartest investment for agility, efficiency, and proactive business intelligence.
About Threat Watch
Threat Watch is a revolutionary cybersecurity intelligence platform meticulously crafted to protect organizations from the dynamic and increasingly complex landscape of cyber threats. In an age where digital assets are constantly under siege, Threat Watch assesses your organization's critical assets, vulnerabilities, and exposures, offering a thorough overview of your cyber health. Its strength lies in real-time insights and automated assessments that empower organizations to quickly identify, prioritize, and mitigate risks. Designed for everyone from small businesses to large enterprises, Threat Watch is the go-to solution for those looking to enhance their cybersecurity defenses. With its intuitive interface and powerful analytics, security teams can make informed, data-driven decisions, ensuring threats are neutralized before they can inflict damage. Experience cybersecurity like never before and uncover your organization's cyber health in a flash with Threat Watch.
Frequently Asked Questions
Karolium FAQ
What makes Karolium different from other low-code/no-code platforms?
Karolium is recognized by Gartner & IDC not just as a development tool, but as a unified enterprise intelligence platform. It uniquely combines application building, integration, operations, and AI services (aPaaS, iPaaS, oPaaS, AIPaaS) into one zero-code environment. It focuses on augmenting core systems with pre-built, composable value-chain solutions at 10X speed, going beyond simple app builders.
Can Karolium integrate with our existing software like SAP or Salesforce?
Absolutely. A core strength of Karolium is its ability to seamlessly augment existing application ecosystems. It is designed for seamless integration with both legacy systems and modern microservices applications, including major ERPs like SAP and CRMs like Salesforce, without requiring you to rip and replace your current investments.
Is Karolium suitable for non-technical business users?
Yes, that's the power of its zero-code technology. The platform is designed for forward-thinking business teams to rapidly build and customize applications without traditional coding. The visual, code-free environment and pre-composed modules empower subject matter experts to create solutions that fit their unique workflows directly.
How does the subscription model work and what does it include?
Karolium is delivered as a managed PaaS-driven SaaS platform with an active subscription. This model provides continuous access to the latest platform innovations, all quarterly solution enhancements, and new value-chain modules. It includes support for unlimited users and offers boundless customization for both pre-packaged and user-composed applications.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for organizations of all sizes, from small businesses to large enterprises. Its scalable features make it an ideal solution for anyone looking to improve their cybersecurity defenses.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced scanning techniques to monitor various dark web forums and marketplaces for stolen credentials and compromised accounts. This proactive approach ensures organizations can act before threats materialize.
Can Threat Watch integrate with existing security tools?
Yes! Threat Watch is designed to seamlessly integrate with a wide range of existing security tools and platforms, enhancing your current cybersecurity framework without disrupting your operations.
Is there a free trial available for Threat Watch?
Absolutely! Threat Watch offers a free scan to help organizations assess their cybersecurity health. This allows potential users to experience the platform's capabilities before making a commitment.
Alternatives
Karolium Alternatives
Karolium is a Gartner-recognized, zero-code platform that lets businesses build custom AI applications at incredible speed. It falls into the development and enterprise intelligence category, empowering teams to create solutions without traditional coding bottlenecks. Users often explore alternatives for various reasons, including budget constraints, specific feature requirements not covered, or a need for a platform that aligns with different technical ecosystems or company size. It's a common step in finding the perfect fit for unique operational needs. When evaluating other options, key considerations should include the true depth of zero-code customization, the strength of AI and analytics capabilities, and how well a platform integrates with your existing software stack. The goal is to find a solution that delivers similar agility and intelligence without compromise.
Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence platform designed to assess organizations' cybersecurity health and identify potential threats. As a vital tool for businesses seeking to enhance their security posture, it provides real-time insights and automated assessments to safeguard assets against the evolving landscape of cyber threats. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with their existing platforms. When exploring alternatives, it is essential to consider features such as real-time monitoring, ease of use, and the ability to integrate with your current security solutions. Choosing the right cybersecurity solution can be daunting, especially with the myriad of options available. Prospective users should look for platforms that offer comprehensive vulnerability analysis, robust analytics, and user-friendly interfaces. The ideal alternative should not only meet your organization's security needs but also provide a seamless experience for your security teams, enabling them to focus on mitigating risks effectively.
