iGPT vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
iGPT instantly turns messy email data into trusted AI answers for enterprise workflows.
Last updated: March 1, 2026
Threat Watch
Instantly evaluate your cybersecurity health and uncover threats with Threat Watch's actionable insights today!.
Last updated: March 1, 2026
Visual Comparison
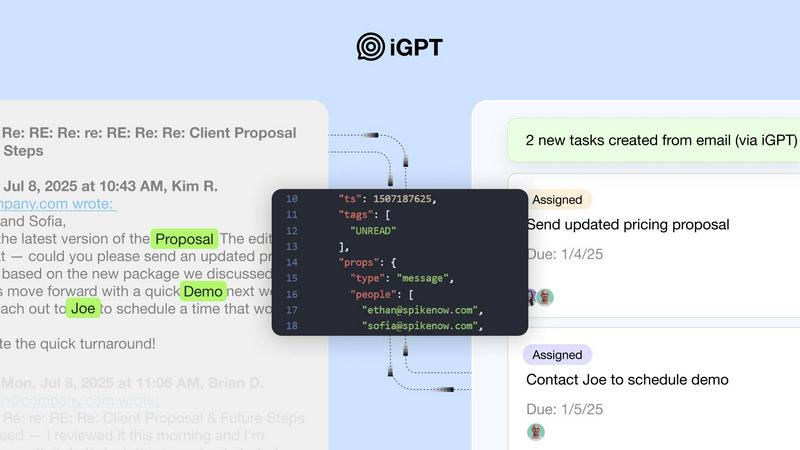
iGPT
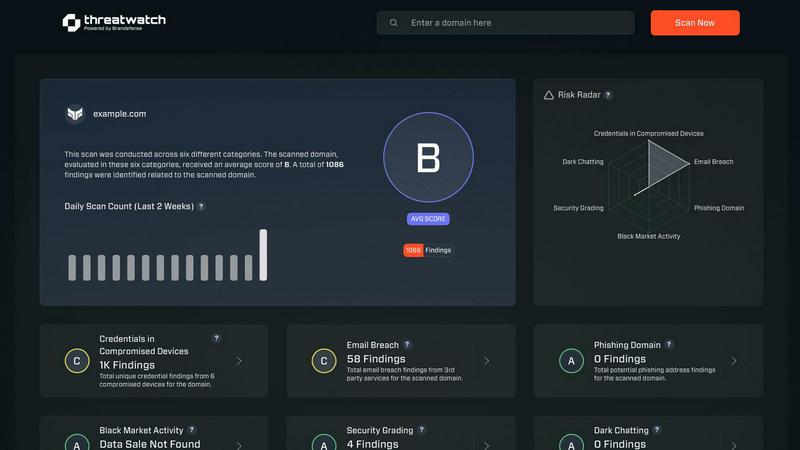
Threat Watch
Feature Comparison
iGPT
Unified Intelligence Endpoint
Ditch the multi-step retrieval and reasoning pipelines. iGPT's single API call seamlessly combines retrieval, context shaping, and advanced reasoning into one powerful request. You provide a natural language query, and it returns a structured, cited answer in roughly 3 seconds, eliminating the need to manage separate systems for parsing, chunking, or vector stores.
Deep Context Engineering
iGPT doesn't just fetch emails; it understands them. The system automatically reconstructs full conversation threads across time and participants, deeply indexes all attachment data (PDFs, spreadsheets, docs), and uses a hybrid retrieval model to find the most relevant information. It then optimally shapes this context for your LLM, delivering precise answers without any manual prompt tuning.
Real-Time Live Indexing
Your data is never stale. iGPT continuously and instantly indexes new messages and attachments as they arrive, ensuring that every query and automated agent operates on the most up-to-date information available. This live sync turns email from a static archive into a dynamic, actionable knowledge base for real-time decision support.
Enterprise-Grade Security & Audit
Built with zero trust from the ground up. iGPT guarantees zero data training, zero data retention post-processing, and provides a full audit trail for every response. With OAuth-only processing and strict Role-Based Access Control (RBAC), your company's sensitive communication data never leaves your control and is fully traceable.
Threat Watch
Real-Time Cyber Threat Monitoring
Stay ahead of potential threats with real-time monitoring that keeps you informed about emerging risks and vulnerabilities. Threat Watch continuously scans your environment, alerting you to any suspicious activities that could compromise your security.
Automated Risk Assessments
Say goodbye to manual risk evaluations. Threat Watch automates the risk assessment process, providing you with timely insights into your organization's vulnerabilities and exposures. This feature allows security teams to prioritize their efforts effectively and allocate resources where they are most needed.
Comprehensive Asset Evaluation
Understand your cyber landscape with an in-depth analysis of your critical assets. Threat Watch evaluates every aspect of your cybersecurity posture, providing a complete view of your strengths and weaknesses, enabling informed decision-making.
Dark Web Monitoring
Uncover threats lurking in the shadows with our Dark Web Monitoring feature. Threat Watch scans dark web forums and marketplaces for stolen credentials and compromised accounts, giving you the ability to take action before these threats affect your organization.
Use Cases
iGPT
AI-Powered Email Assistants
Build intelligent agents that can draft replies, prioritize your inbox, summarize long threads, and even take action—all with a complete, nuanced understanding of the entire email history and attached files. These assistants act with full context, dramatically boosting productivity for teams across sales, support, and executive functions.
Automated Workflow Orchestration
Transform email threads directly into structured tasks, deadlines, and approval processes. Automatically flag stalled conversations, extract action items with owners and due dates, and push data into project management or CRM tools. Turn communication into automated workflow, eliminating manual triage and follow-up.
Customer Support Copilots
Empower support teams with agents that can instantly rebuild a customer's entire story. By analyzing long email chains, tone shifts, and all related attachments, these copilots provide agents with immediate, cited context to resolve issues faster and deliver consistently exceptional, informed service.
Compliance & CRM Intelligence
Automatically extract critical decisions, approvals, and deal momentum directly from email threads for a flawless audit trail. For sales teams, iGPT agents can monitor communication to update CRM records, forecast risks, and identify key stakeholders and sentiment, turning inbox activity into strategic business intelligence.
Threat Watch
Small Business Cybersecurity Enhancement
Small businesses often lack the resources for extensive cybersecurity measures. Threat Watch provides an affordable and effective way for them to identify vulnerabilities and enhance their security posture, ensuring they are protected from cyber threats.
Enterprise-Level Risk Management
Large enterprises face complex security challenges. Threat Watch streamlines risk management processes by providing real-time insights and automated assessments, allowing security teams to focus on strategic initiatives while effectively managing risks.
Incident Response Preparation
Being prepared for an incident is crucial. Threat Watch equips organizations with the tools needed for rapid incident response. By continuously monitoring threats and vulnerabilities, companies can respond swiftly and effectively to mitigate damage.
Compliance and Regulatory Assurance
Organizations need to comply with various cybersecurity regulations. Threat Watch helps in maintaining compliance by providing detailed reports and assessments, ensuring that organizations meet necessary standards and protocols.
Overview
About iGPT
iGPT is the game-changing email intelligence API that's setting a new standard for how enterprises build with AI. Forget clunky parsing and fragile prompt chains—this is the infrastructure that finally makes email data work for you. iGPT provides a secure, auditable pipeline that instantly turns messy email threads and complex attachments into trusted, context-aware answers that agents and workflows can actually use. It's built for engineering teams at forward-thinking companies who are tired of AI breaking where real work happens: in the inbox. With its revolutionary unified endpoint, you bypass months of complex data engineering. Just connect your email sources, and iGPT handles the rest: real-time indexing, deep attachment processing, intelligent thread reconstruction, and optimized context delivery. Join the thousands of developers who are already shipping intelligent email assistants, automated workflows, and powerful copilots in days, not months, and unlock the strategic insights buried in your organization's most critical communication channel.
About Threat Watch
Threat Watch is a revolutionary cybersecurity intelligence platform meticulously crafted to protect organizations from the dynamic and increasingly complex landscape of cyber threats. In an age where digital assets are constantly under siege, Threat Watch assesses your organization's critical assets, vulnerabilities, and exposures, offering a thorough overview of your cyber health. Its strength lies in real-time insights and automated assessments that empower organizations to quickly identify, prioritize, and mitigate risks. Designed for everyone from small businesses to large enterprises, Threat Watch is the go-to solution for those looking to enhance their cybersecurity defenses. With its intuitive interface and powerful analytics, security teams can make informed, data-driven decisions, ensuring threats are neutralized before they can inflict damage. Experience cybersecurity like never before and uncover your organization's cyber health in a flash with Threat Watch.
Frequently Asked Questions
iGPT FAQ
How does iGPT handle data privacy and security?
iGPT is engineered for the enterprise with a foundational commitment to security. It operates on a zero-data-training and zero-data-retention policy, meaning your emails and attachments are never used to train models or stored after processing. All inferences happen in-memory. Access is strictly controlled via OAuth and RBAC, ensuring full auditability and data sovereignty.
What's the difference between iGPT and building my own RAG system?
Building a custom Retrieval-Augmented Generation system for email requires months of work: parsing MIME, chunking text, managing vector stores, tuning prompts, and maintaining pipelines. iGPT replaces all that complexity with a single API call. It handles the entire context engineering lifecycle—real-time ingestion, hybrid retrieval, thread reconstruction—so you can ship production agents in days.
Can iGPT process attachments, and what file types are supported?
Absolutely. Deep attachment processing is a core strength. iGPT automatically extracts text, data, and structure from a wide range of documents within emails, including PDFs, spreadsheets (like Excel and Sheets), presentations, and word processing documents. This content is fully indexed and integrated into the context of the email thread for comprehensive answers.
How quickly can I integrate and start testing iGPT?
Integration is designed to be immediate. With a ready-to-use SDK, a live playground to test queries, and a simple unified endpoint, developers can connect data sources and get their first contextual answers in minutes. iGPT offers $10 in free credits to start experimenting with no credit card required, so you can validate its power instantly.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for organizations of all sizes, from small businesses to large enterprises. Its scalable features make it an ideal solution for anyone looking to improve their cybersecurity defenses.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced scanning techniques to monitor various dark web forums and marketplaces for stolen credentials and compromised accounts. This proactive approach ensures organizations can act before threats materialize.
Can Threat Watch integrate with existing security tools?
Yes! Threat Watch is designed to seamlessly integrate with a wide range of existing security tools and platforms, enhancing your current cybersecurity framework without disrupting your operations.
Is there a free trial available for Threat Watch?
Absolutely! Threat Watch offers a free scan to help organizations assess their cybersecurity health. This allows potential users to experience the platform's capabilities before making a commitment.
Alternatives
iGPT Alternatives
iGPT is a leading email intelligence API that falls squarely into the Business Intelligence category. It transforms raw email data into structured, actionable insights, powering AI-driven workflows for enterprises. By securely parsing conversations and attachments, it provides the context needed for automation and smarter decision-making. Users often explore alternatives for several key reasons. Budget constraints, specific feature requirements not covered, or the need for integration with a different tech stack can all drive the search. Some teams might seek a more niche solution or a platform with a different pricing model, like a freemium tier or usage-based billing. When evaluating other options, focus on core capabilities. Security and compliance should be non-negotiable, especially for email data. Look for robust real-time processing, the quality of contextual understanding, and ease of integration. The best alternative will offer transparent sourcing of insights and fit seamlessly into your existing enterprise workflow without creating complexity.
Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence platform designed to assess organizations' cybersecurity health and identify potential threats. As a vital tool for businesses seeking to enhance their security posture, it provides real-time insights and automated assessments to safeguard assets against the evolving landscape of cyber threats. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with their existing platforms. When exploring alternatives, it is essential to consider features such as real-time monitoring, ease of use, and the ability to integrate with your current security solutions. Choosing the right cybersecurity solution can be daunting, especially with the myriad of options available. Prospective users should look for platforms that offer comprehensive vulnerability analysis, robust analytics, and user-friendly interfaces. The ideal alternative should not only meet your organization's security needs but also provide a seamless experience for your security teams, enabling them to focus on mitigating risks effectively.
