CMMC ROI vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
CMMC ROI
Unlock your DoD contracting potential by accurately calculating your CMMC compliance ROI and investment strategies.
Last updated: March 1, 2026
Threat Watch
Instantly evaluate your cybersecurity health and uncover threats with Threat Watch's actionable insights today!.
Last updated: March 1, 2026
Visual Comparison
CMMC ROI

Threat Watch
Feature Comparison
CMMC ROI
Personalized Investment Analysis
CMMC ROI offers customized investment calculations based on your organization's specific parameters, including size, revenue, and compliance status. This means you receive a tailored investment forecast that reflects your unique business scenario.
Comprehensive ROI Calculation
The calculator not only provides a breakdown of implementation and maintenance costs but also factors in potential revenue protection and breach cost avoidance, ensuring you understand your actual return on investment.
Real-Time Risk Assessment
With CMMC ROI, businesses can assess their contract value at risk without compliance and the associated financial implications. This feature empowers organizations to see the tangible risks of non-compliance and motivates timely action.
Implementation Timeline Guidance
CMMC ROI outlines a clear 12-month roadmap to achieving CMMC Level 2 certification. This includes phases like gap assessment, remediation, documentation, and final certification, allowing organizations to plan and allocate resources effectively.
Threat Watch
Real-Time Cyber Threat Monitoring
Stay ahead of potential threats with real-time monitoring that keeps you informed about emerging risks and vulnerabilities. Threat Watch continuously scans your environment, alerting you to any suspicious activities that could compromise your security.
Automated Risk Assessments
Say goodbye to manual risk evaluations. Threat Watch automates the risk assessment process, providing you with timely insights into your organization's vulnerabilities and exposures. This feature allows security teams to prioritize their efforts effectively and allocate resources where they are most needed.
Comprehensive Asset Evaluation
Understand your cyber landscape with an in-depth analysis of your critical assets. Threat Watch evaluates every aspect of your cybersecurity posture, providing a complete view of your strengths and weaknesses, enabling informed decision-making.
Dark Web Monitoring
Uncover threats lurking in the shadows with our Dark Web Monitoring feature. Threat Watch scans dark web forums and marketplaces for stolen credentials and compromised accounts, giving you the ability to take action before these threats affect your organization.
Use Cases
CMMC ROI
Small Contractor Compliance Planning
For small contractors with 1-50 employees, CMMC ROI provides clarity on the investment required to achieve compliance, helping them secure vital DoD contracts with a manageable budget.
Medium-Sized Business Decision Making
Medium contractors, with revenues of up to $10 million, can leverage CMMC ROI to understand their investment landscape. This ensures they can make strategic decisions that align with their growth objectives while remaining compliant.
Large Prime Contractor Strategy
Large contractors can utilize CMMC ROI to calculate substantial investments required for Level 3 compliance. This enables them to justify expenses to stakeholders by demonstrating the potential for a 340% ROI over five years.
Risk Mitigation for Technology Firms
Technology firms that work with DoD contracts can use CMMC ROI to evaluate their compliance status and calculate the financial risks associated with breaches. This helps them prioritize cybersecurity investments in a data-driven manner.
Threat Watch
Small Business Cybersecurity Enhancement
Small businesses often lack the resources for extensive cybersecurity measures. Threat Watch provides an affordable and effective way for them to identify vulnerabilities and enhance their security posture, ensuring they are protected from cyber threats.
Enterprise-Level Risk Management
Large enterprises face complex security challenges. Threat Watch streamlines risk management processes by providing real-time insights and automated assessments, allowing security teams to focus on strategic initiatives while effectively managing risks.
Incident Response Preparation
Being prepared for an incident is crucial. Threat Watch equips organizations with the tools needed for rapid incident response. By continuously monitoring threats and vulnerabilities, companies can respond swiftly and effectively to mitigate damage.
Compliance and Regulatory Assurance
Organizations need to comply with various cybersecurity regulations. Threat Watch helps in maintaining compliance by providing detailed reports and assessments, ensuring that organizations meet necessary standards and protocols.
Overview
About CMMC ROI
CMMC ROI is a cutting-edge investment calculator developed by BomberJacket Networks, specifically designed to help DoD contractors navigate the complexities of CMMC compliance. As the Department of Defense enforces cybersecurity regulations starting in Q4 2025, understanding the true costs and benefits of compliance has never been more crucial. This tool transforms what is often viewed as a burdensome expense into a strategic asset. CMMC ROI provides tailored, data-driven analyses that allow organizations—ranging from small subcontractors to large prime contractors—to accurately forecast their five-year investment, payback periods, and potential returns. With over 20 years of expertise in the field and a 99% success rate, CMMC ROI enables businesses to make informed decisions that can safeguard their contracts and enhance their competitiveness in the defense industrial base, demonstrating that compliance is not just about meeting regulations; it's about securing an impressive average ROI of 340% over five years.
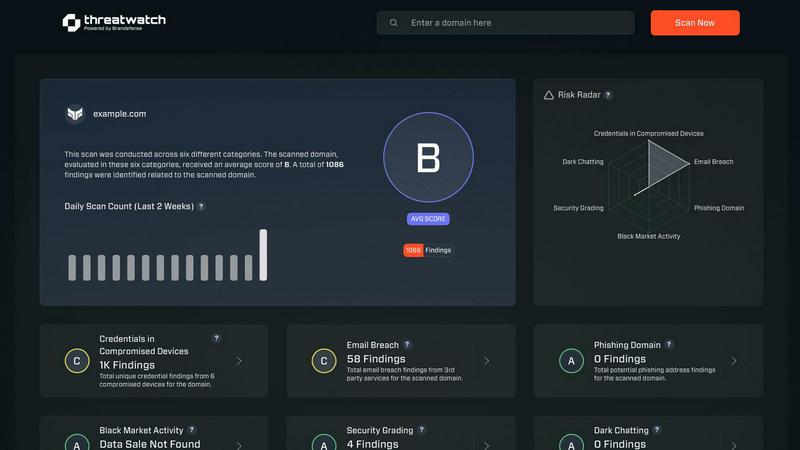
About Threat Watch
Threat Watch is a revolutionary cybersecurity intelligence platform meticulously crafted to protect organizations from the dynamic and increasingly complex landscape of cyber threats. In an age where digital assets are constantly under siege, Threat Watch assesses your organization's critical assets, vulnerabilities, and exposures, offering a thorough overview of your cyber health. Its strength lies in real-time insights and automated assessments that empower organizations to quickly identify, prioritize, and mitigate risks. Designed for everyone from small businesses to large enterprises, Threat Watch is the go-to solution for those looking to enhance their cybersecurity defenses. With its intuitive interface and powerful analytics, security teams can make informed, data-driven decisions, ensuring threats are neutralized before they can inflict damage. Experience cybersecurity like never before and uncover your organization's cyber health in a flash with Threat Watch.
Frequently Asked Questions
CMMC ROI FAQ
What is CMMC ROI?
CMMC ROI is a data-driven investment calculator that helps DoD contractors assess the costs and potential returns associated with achieving CMMC compliance, ensuring informed decision-making.
How does CMMC ROI calculate ROI?
The tool calculates ROI by assessing protected value, which includes 5-year DoD revenue and potential breach cost avoidance, against the total estimated investment for compliance.
Who can benefit from using CMMC ROI?
CMMC ROI is designed for businesses of all sizes, from small subcontractors to large prime contractors, particularly those involved in DoD contracting and needing to achieve CMMC compliance.
What is the average ROI for CMMC compliance?
The average ROI for organizations achieving CMMC compliance is approximately 340% over five years, showcasing the financial benefits of strategic compliance investments.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for organizations of all sizes, from small businesses to large enterprises. Its scalable features make it an ideal solution for anyone looking to improve their cybersecurity defenses.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced scanning techniques to monitor various dark web forums and marketplaces for stolen credentials and compromised accounts. This proactive approach ensures organizations can act before threats materialize.
Can Threat Watch integrate with existing security tools?
Yes! Threat Watch is designed to seamlessly integrate with a wide range of existing security tools and platforms, enhancing your current cybersecurity framework without disrupting your operations.
Is there a free trial available for Threat Watch?
Absolutely! Threat Watch offers a free scan to help organizations assess their cybersecurity health. This allows potential users to experience the platform's capabilities before making a commitment.
Alternatives
CMMC ROI Alternatives
CMMC ROI is a powerful investment calculator that enables businesses to quantify their compliance costs and benefits in a data-driven manner. Positioned within the Business Intelligence category, it transforms CMMC compliance from merely a regulatory hurdle into a strategic asset, helping organizations secure vital DoD contracts. Users often seek alternatives due to various reasons, including pricing structures, specific feature sets, or the need for integration with existing platforms. When searching for an alternative, prioritize tools that offer personalized calculations, scenario-based modeling, and clear visualizations to ensure you can make informed financial decisions regarding your cybersecurity investments.
Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence platform designed to assess organizations' cybersecurity health and identify potential threats. As a vital tool for businesses seeking to enhance their security posture, it provides real-time insights and automated assessments to safeguard assets against the evolving landscape of cyber threats. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with their existing platforms. When exploring alternatives, it is essential to consider features such as real-time monitoring, ease of use, and the ability to integrate with your current security solutions. Choosing the right cybersecurity solution can be daunting, especially with the myriad of options available. Prospective users should look for platforms that offer comprehensive vulnerability analysis, robust analytics, and user-friendly interfaces. The ideal alternative should not only meet your organization's security needs but also provide a seamless experience for your security teams, enabling them to focus on mitigating risks effectively.
